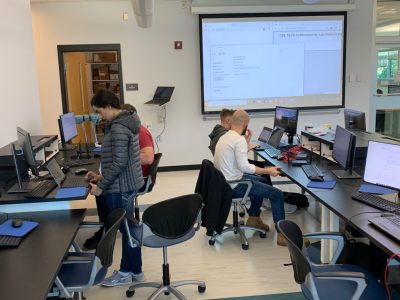
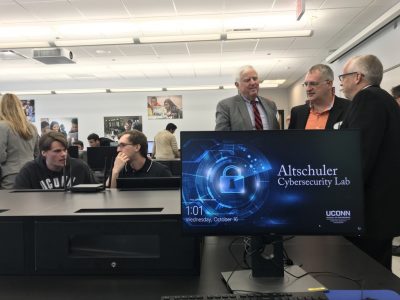
This semester I’ve been focusing most of my attention on preparing a new teaching laboratory at UConn. The lab was dedicated today and I figure this is as good a chance as any to talk about it. The lab was initiated thanks to a wonderful endowment established by Sam and Steve Altschuler who are both UConn Alumni (’50 and ’54). The endowment is designed to keep us up to date on equipment as cybersecurity threats change. This lab has two primary differences from my traditional teaching:
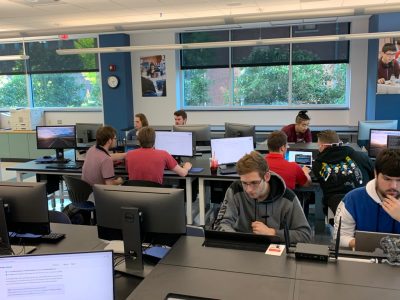
- There’s no lecture, all entire contact time is students working.
- Students learn by working in projects, they are free to search the web for anything, modeling how they actually will work in practice.
- The class is designed for general scientists and engineers, not cybersecurity experts. The goal is to create enough exposure to the issues to make people stop and think when they make a new web app or backend database. As a side benefit we will get more people interested in cybersecurity as a career.
The topics we are covering this semester are:
- Authentication and password cracking
- Wired network sniffing, protocol reverse engineering
- Wireless hijacking
- The USB interface, faking a keyboard and the powers of physical access.
- Memory safety and why it matters
- The wild west of IoT
The lab we’re currently working on uses a setup of a Raspberry PI and Pineapple tetra as the primary components. The pineapple is used to create a rogue wireless network and to deauth clients from a legitimate network. Students are then faking DNS and standing up a malicious website to collect credentials. This is all achievable in a few hours with a couple hundred dollars of equipment. I’ve been amazed by the engagement so far. I keep being surprised by how much work it is to set up a good lab. I know lecturing is easier, my hope is that brings a unique experience to students.
Ben